SOC 2 business continuity controls are the specific policies, procedures, and technical systems an organization implements to ensure its services remain available and its operational commitments are met during and after a significant disruption. These controls are a core component of the AICPA’s Trust Services Criteria, particularly Availability, and require organizations to develop, test, and maintain a Business Continuity Plan (BCP) and a Disaster Recovery (DR) plan to manage potential incidents ranging from technological failures to natural disasters.
These plans are not merely procedural documents; for a SOC 2 audit, they represent an organization’s demonstrable capability to maintain service levels and protect customer data. This includes both a Business Continuity Plan (BCP), which addresses maintaining essential business functions, and a Disaster Recovery (DR) plan, which details the technical processes for restoring IT infrastructure and data.
Defining Business Continuity in a SOC 2 Context
From a SOC 2 compliance perspective, business continuity is the documented and tested ability of an organization to withstand disruptive events and maintain the availability of its systems and services as committed to customers. It is a direct reflection of an organization’s risk management maturity and its capacity to uphold its Service Level Agreements (SLAs). An auditor evaluates these controls to verify that a company has a structured, proactive approach to resilience, rather than a reactive one.
A successful SOC 2 audit requires demonstrating that your business continuity strategy is designed to address specific threats identified in a formal risk assessment, covering events from cyberattacks to critical system failures.

These controls are the backbone of the AICPA’s Availability Trust Services Criterion. The entire purpose of the Availability criterion is to prove that a system is accessible for operation and use as committed or agreed. Without a robust, tested business continuity framework, an organization cannot credibly assert that it meets this criterion.
The BCP and DR Distinction
For a SOC 2 audit, distinguishing between the Business Continuity Plan and the Disaster Recovery plan is critical, as an auditor will expect to see evidence for both. These two components address different facets of resilience.
- Business Continuity Plan (BCP): This is the strategic, business-focused plan that outlines procedures for sustaining essential functions during a disruption. For SOC 2 purposes, this means proving you can manage personnel, critical processes, and stakeholder communications to continue operations.
- Disaster Recovery (DR) Plan: This is the tactical, IT-centric plan that provides explicit, technical instructions for restoring systems, applications, and data. This plan directly supports the BCP by detailing the “how” of technical recovery, such as failover procedures and data restoration steps.
Why does this distinction matter for someone pursuing SOC 2? An auditor needs to see that you have not only a plan to recover your technology (DR) but also a comprehensive strategy to keep the business operational and meet customer commitments (BCP). For example, your BCP might dictate a four-hour recovery time for customer support operations. The DR plan would then provide the specific technical steps—like failing over the CRM to a secondary site—required to meet that objective, providing tangible evidence that the BCP is achievable.
Why This Matters for SOC 2
Establishing a clear BCP/DR framework is a foundational requirement for a strong SOC 2 posture. Auditors will not just review the existence of these plans; they will scrutinize them for completeness, test them for operational effectiveness, and verify that they align with business objectives defined in a Business Impact Analysis (BIA). A well-defined BCP and DR plan signal that your organization has implemented mature, risk-based controls to ensure service availability.
For any company pursuing SOC 2, these controls are non-negotiable as they provide the auditable evidence that you can fulfill the uptime and data protection commitments made in your SLAs. A weak or untested BCP is viewed by an auditor not just as a planning deficiency but as a critical failure in risk management that directly impacts your ability to meet the Availability criterion.
How Business Continuity Maps to SOC 2 Criteria
For SOC 2, a business continuity plan is not a standalone artifact; it is an integral control mechanism that is directly mapped to the AICPA’s Trust Services Criteria. These controls provide the necessary evidence to prove that an organization can maintain its service commitments, especially during adverse events. This direct linkage transforms an internal BCDR plan into a cornerstone of your SOC 2 audit evidence, demonstrating a mature approach to risk and resilience.
The most prominent connection is to the Availability criterion, which is centered on ensuring systems are operational and usable as defined in contracts or SLAs. However, business continuity also has a critical link to the Common Criteria (CC) for Security, which establish foundational requirements for all SOC 2 audits.
The Availability Criterion Connection
The Availability criterion is the primary domain where your business continuity plan is evaluated. A SOC 2 auditor uses this criterion to assess whether you have implemented sufficient controls to manage and mitigate disruptions to service.
Criterion A1.2 is the most direct requirement:
“The entity authorizes, designs, develops or acquires, implements, configures, documents, tests, approves, and maintains environmental protections, software, data backup processes, and recovery infrastructure to meet its availability objectives.”
Why does this matter for someone pursuing SOC 2? This criterion requires you to provide evidence for the entire lifecycle of your recovery capabilities. It is insufficient to state that backups exist; you must demonstrate through documentation and test results that you test your data backup processes, maintain the recovery infrastructure, and have defined procedures for their use. Your Recovery Time Objectives (RTOs) and Recovery Point Objectives (RPOs) become the measurable benchmarks against which an auditor will assess your plan’s effectiveness. You can dig into the full set of requirements by exploring the SOC 2 Trust Services Criteria in more detail.
The Role of Common Criteria in Continuity
While Availability is the focal point, several Common Criteria are also directly supported by strong business continuity controls. These criteria address system monitoring, incident response, and risk management—all integral to handling a crisis.
For instance, CC7.5 requires the entity to monitor for, evaluate, and communicate security incidents. A major business continuity event, such as a ransomware attack or a catastrophic system failure, qualifies as a severe security incident. Your BCDR plan serves as the operational playbook for your incident response team, ensuring a structured approach to detecting the issue, containing its impact, and restoring services in line with your objectives.
Why does this matter for someone pursuing SOC 2? This link demonstrates that your business continuity plan is not isolated from your security program. An auditor will look for this integration as proof of a holistic risk management strategy. A business continuity event often triggers security incident response procedures, and your ability to execute both in a coordinated manner is a sign of a mature control environment.
Mapping Business Continuity Controls to SOC 2 Trust Services Criteria
This table connects specific Business Continuity and Disaster Recovery (BCDR) activities to the AICPA Trust Services Criteria (TSCs) they support, explaining why each one is critical for your SOC 2 audit.
| BCDR Activity | Relevant Trust Services Criteria (TSC) | Why It Matters for Your SOC 2 Audit |
|---|---|---|
| Defining RTOs and RPOs | Availability (A1.1, A1.2) | Provides auditable evidence that you have established clear, measurable objectives for service restoration that align with customer commitments and SLAs. |
| Implementing Data Backup Strategy | Availability (A1.2) | Provides direct evidence of your technical capability to recover data, a core requirement for proving system recoverability and meeting RPOs. |
| Conducting Failover Testing | Availability (A1.2), Common Criteria (CC7.3) | Demonstrates the operating effectiveness of your DR plan. Auditors require this proof to verify that your recovery mechanisms function as designed under real-world conditions. |
| Business Impact Analysis (BIA) | Common Criteria (CC3.1, CC3.2) | Justifies your continuity strategy by identifying mission-critical systems and the potential impact of their failure, directly linking controls to business objectives and risk. |
| Incident Response Plan Testing | Common Criteria (CC7.3, CC7.5) | Confirms that your team can effectively execute the BCP/DR plan during a simulated event, validating both the plan’s procedures and personnel’s readiness. |
This mapping is your key to a successful audit. When you frame your business continuity work through the lens of the TSCs, your internal processes transform into powerful, auditable evidence. This approach shows a mature grasp of risk and a proactive commitment to reliability—which is exactly what auditors (and your customers) are looking for.
Building a SOC 2 Compliant Business Continuity Plan
To build a business continuity plan (BCP) that satisfies SOC 2 requirements, you must begin with two foundational analyses: a Business Impact Analysis (BIA) and a formal Risk Assessment. These are not administrative formalities; they are the strategic bedrock of your entire resilience strategy and are required by the Common Criteria (specifically CC3.1 and CC3.2). An auditor will request these documents first to understand the rationale behind your continuity controls and how you identified critical systems and prioritized threats.
The BIA is the methodical process of identifying your most critical business processes and the systems that support them. More importantly, it quantifies the operational and financial impact of a disruption over time. This analysis is the sole source for defining two of the most critical metrics in your plan: your Recovery Time Objectives (RTOs) and Recovery Point Objectives (RPOs).
Defining Your Recovery Objectives
RTO and RPO are not abstract technical goals; they are concrete, measurable commitments that form the basis of your SOC 2 audit evidence for the Availability criterion. They must be formally documented, approved by management, and directly traceable to the findings of your BIA.
- Recovery Time Objective (RTO): This is the maximum acceptable period of time a system can be offline following a disruption. If your BIA determines a critical application must be restored within one hour to avoid significant business impact, its RTO is one hour.
- Recovery Point Objective (RPO): This defines the maximum acceptable amount of data loss, measured in time. An RPO of 15 minutes means your DR plan must be capable of restoring all data to a state no more than 15 minutes prior to the incident.
One practical approach that auditors increasingly expect is tiered RTO and RPO targets rather than a single number applied to every system. Not every component of your product carries the same recovery urgency, and differentiating by criticality makes the plan more credible. As a reference point, current cloud DR practice groups systems into tiers roughly as follows: mission-critical systems such as payment processing and core authentication APIs target near-zero RTO and RPO using multi-site active-active architectures; business-critical systems such as CRM and customer-facing APIs target RTO under 15 minutes using warm standby; internal operational systems can tolerate RTO of two to four hours via automated backup and restore; non-critical systems such as dev environments can tolerate eight or more hours using cold storage. Your BIA should drive which tier each system falls into, and your architecture must match those commitments.
For most SaaS companies operating on cloud infrastructure and committing to 99.9% uptime SLAs, warm standby is the practical minimum for customer-facing systems. If your architecture relies on manual failover processes, auditors will note the gap between your stated RTO and your realistic recovery capability during any incident that occurs at an inconvenient time.
Why does this matter for someone pursuing SOC 2? An auditor will rigorously examine these metrics. They will demand evidence that your technical controls, such as backup frequencies, replication technologies, and restoration procedures, are designed, implemented, and tested to consistently meet these documented objectives. Any misalignment between your stated RTO/RPO and your tested capabilities will result in an audit finding.
This is how your business continuity and disaster recovery (BCDR) plan directly proves you meet the Availability and Security criteria in the SOC 2 framework.
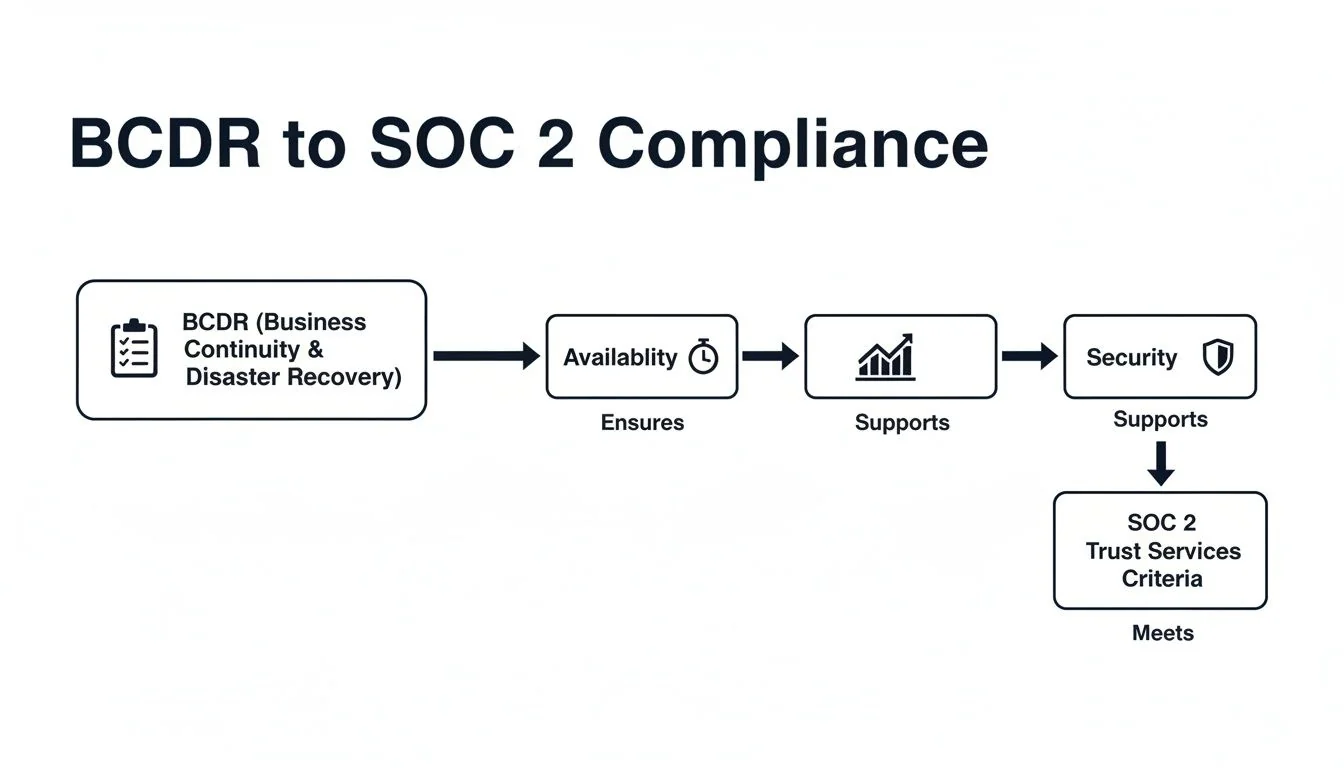
As you can see, a solid BCDR plan isn’t just a “nice-to-have.” It’s the starting point for proving both service uptime and a secure environment, which are non-negotiable for passing a SOC 2 audit.
Core Components of the Plan
With your BIA completed and recovery objectives defined, you can construct the BCP and Disaster Recovery (DR) plan. This is where you translate strategic decisions into an actionable playbook that your team can execute during an incident.
A key component is the formal designation of an incident response team with clearly defined roles and responsibilities. The plan must specify who has the authority to declare a disaster, who leads technical recovery efforts, and who is responsible for internal and external communications. Using a detailed business continuity planning checklist can ensure all critical elements are included.
Why does this matter for someone pursuing SOC 2? From an auditor’s perspective, if a procedure is not documented, it does not exist as a formal control. Your BCP must contain explicit, step-by-step procedures for everything from activating the incident response team and executing data backups to restoring systems and communicating with stakeholders. These documented components provide the evidence an auditor needs to assess the design of your controls for a Type 1 report and serve as the baseline for testing effectiveness in a Type 2 report. This documentation directly addresses the requirements of the Availability criterion by proving that your continuity controls are deliberate, structured, and repeatable.
How to Implement and Test Your Continuity Controls
A documented business continuity plan is only a statement of intent. For SOC 2 compliance, especially for a Type 2 report, you must provide evidence that the plan is operationally effective. This is achieved through implementation and rigorous testing, which transforms your documented strategy into a proven, reliable capability. You must conduct exercises that validate both your business-level BCP and your technical DR plan to demonstrate that you can meet your recovery objectives.
Why does this matter for someone pursuing SOC 2? An auditor requires objective evidence that your controls work as designed. Untested plans are considered a significant control deficiency. The records from your tests—such as after-action reports and system logs—are primary artifacts that auditors examine to verify the operating effectiveness of your controls over the audit period.

Conducting Effective Tabletop Exercises
A tabletop exercise is a structured, discussion-based session where the incident response team walks through a simulated disaster scenario. The objective is not to perform a technical recovery but to validate the procedures, roles, and communication flows outlined in the BCP.
Here is an actionable process for a SOC 2-compliant exercise:
- Define a Specific Test Objective: Frame the objective in measurable terms. For example: “Verify the incident response team can execute the customer communication plan and provide an initial status update within 30 minutes of a declared incident, as required by the BCP.”
- Develop a Plausible Scenario: Base the scenario on your risk assessment. A realistic event, such as a major cloud provider outage or a targeted ransomware attack, provides a more effective test than a generic or improbable one.
- Facilitate and Document Rigorously: A facilitator should guide the team through the scenario, prompting decisions based on the BCP. A dedicated scribe must take detailed notes on actions taken, decisions made, and any identified gaps or weaknesses.
- Produce an After-Action Report: This is a critical piece of audit evidence. The report must summarize the exercise, detail what worked, and list specific, actionable recommendations with assigned owners and due dates for improving the BCP.
This entire process directly provides evidence for criteria like CC7.3, which requires that response plans are tested. The after-action report and subsequent remediation actions demonstrate a mature, continuous improvement cycle for your controls.
Validating Technical Recovery Procedures
While tabletop exercises test human processes, technical validation tests your systems’ ability to recover. These hands-on tests are designed to prove you can meet your RTOs and RPOs. A SOC 2 auditor will demand tangible evidence, not just assertions, that these tests were successfully performed.
Key technical tests include:
- Backup Integrity Verification: Regularly perform automated or manual checks to ensure backup files are not corrupted and are complete. Automate checksum comparisons and alert on failures, rather than relying on manual spot checks.
- Full System Restoration: Periodically restore a critical system from backup to a non-production environment. Document the entire process, including start time, end time, and any issues encountered, to validate your RTO.
- Database Recovery Testing: Restore a critical database from a backup and perform data integrity checks to prove you can meet your RPO. For databases with high write volume, point-in-time recovery should be enabled and tested, not just assumed to function.
- Failover Testing: For high-availability environments, intentionally trigger a failover to your secondary infrastructure to test the automatic or manual failover process and validate its effectiveness.
On testing frequency: the AICPA’s Availability criterion (A1.3) requires at least annual DR testing, and that remains the floor. In practice, auditors and enterprise buyers increasingly expect more. For SaaS companies serving regulated industries, quarterly DR tests that rotate across different failure scenarios (region failure, database failure, application-layer failure) provide significantly stronger evidence than a single annual exercise. Many teams also supplement scheduled tests with lightweight weekly or bi-weekly spot restorations of subsets of data to staging, building a continuous evidence trail across the observation period rather than a single annual data point.
Build your test log to capture what auditors actually sample: test date, dataset or environment, test type, RPO/RTO target, actual result, tester name, and any corrective actions taken. Auditors will ask to see backup success logs from specific sampled dates, and they will check whether failures triggered alerts and were remediated. A test that reveals a gap is not a problem if you can show the gap was fixed. A gap with no remediation record is a finding.
Why does this matter for someone pursuing SOC 2? A common failure is assuming backups are functional simply because the software reports success. According to recovery research, organizations recover only about 57% of affected data on average when restoration has never been tested beforehand. SOC 2 auditors require proof of successful restoration, not successful backup job completion. Screenshots, system logs, and detailed test records are non-negotiable evidence for a Type 2 report. This hands-on testing directly supports Availability criterion A1.2, which requires that recovery capabilities are tested to meet availability objectives.
Gathering Evidence for Your SOC 2 Audit
For a SOC 2 audit, evidence is the sole determinant of compliance. Your business continuity controls must be supported by an organized collection of artifacts that prove your plans are not just well-designed but are operating effectively. This evidence demonstrates that your resilience strategy is an integral, tested, and maintained component of your control environment, directly supporting the Availability and Security Trust Services Criteria.
The required evidence differs based on whether you are undergoing a Type 1 audit, which assesses the design of controls at a point in time, or a Type 2 audit, which assesses their operating effectiveness over a period.
Evidence for a SOC 2 Type 1 Report
A Type 1 report evaluates the suitability of the design of your controls. The auditor is examining your BCDR framework to determine if it is logical, complete, and aligned with SOC 2 criteria. The evidence required is primarily your foundational planning documentation.
Why does this matter for someone pursuing SOC 2? These documents are the blueprint of your resilience program. Without them, you cannot demonstrate to an auditor that you have a formally designed control environment to meet the criteria.
Essential Type 1 Evidence:
- Business Continuity Plan (BCP): The complete, management-approved document.
- Disaster Recovery (DR) Plan: The detailed technical plan for IT infrastructure and data restoration.
- Business Impact Analysis (BIA): The report identifying critical systems and defining RTOs/RPOs.
- Risk Assessment: The formal analysis of threats that justifies your continuity strategy.
- Incident Response Team Roster: A current list of members, roles, responsibilities, and contact information.
This collection of documents forms the foundation of your audit. You can get more details on how these documents fit together in our complete guide on SOC 2 documentation.
Evidence for a SOC 2 Type 2 Report
A Type 2 report requires proof that your controls have operated effectively over a period (typically 6 to 12 months). This demands a more extensive and dynamic set of evidence demonstrating that your plans have been tested, reviewed, and maintained.
Why does this matter for someone pursuing SOC 2? This evidence proves your controls are not just theoretical but are functioning in practice. Auditors will scrutinize these records to confirm that the activities described in your plans actually occurred and were effective.
Critical Type 2 Evidence:
- Tabletop Exercise Records: All documentation related to BCP tests, including meeting invitations, agendas, sign-in sheets, detailed minutes, and the final after-action report with evidence of follow-up on remediation tasks.
- Technical Test Results: Tangible proof of DR tests, such as screenshots of successful data restorations, system logs from failover tests, and reports from backup integrity checks including timestamps. Auditors will sample specific dates within your observation window and ask for the corresponding logs, not just a summary report from one annual test.
- BCP/DR Plan Update History: A change log or version history demonstrating that plans are reviewed and updated annually or after significant changes (for example, new systems or test findings).
- Employee Training Records: Attendance logs or training materials showing that the incident response team has been trained on the continuity plans.
A point that catches many teams off-guard: the single most common BC/DR exception auditors issue is a well-written plan with no test results, or test results that lack the detail to be useful. A record that says “DR test conducted, systems recovered” without recovery timestamps or comparison against your RTOs does not give the auditor what they need. Every test result should include the scenario, the date, which systems were tested, actual recovery times measured against your stated targets, and any gaps found with remediation tracking.
Evidence continuity across the full observation period matters as much as any individual artifact. Auditors are increasingly looking for evidence that flows consistently across all 6 to 12 months rather than a cluster of documents assembled in the weeks before the audit. Compliance tooling that continuously pulls configuration state, backup job logs, and test records from source systems produces more defensible evidence than manually assembled screenshots, because the source, generation date, and data boundaries are clear. If you are not yet using automation for evidence collection, at minimum maintain a running test log that records each backup spot-restoration, failover test, and tabletop exercise as they happen, with named owners and timestamps.
For a Type 2 audit, the narrative your evidence presents is what matters. An after-action report from a tabletop exercise that identifies three weaknesses is not a failure; it becomes powerful evidence of a mature control environment if you can also show the corresponding change management tickets or remediation plans created to address those weaknesses. This demonstrates a functioning control loop of testing, identification, and remediation, which is exactly what an auditor needs to see.
Strong SOC 2 business continuity controls are ultimately defined not by the plan itself, but by the tangible proof that the plan is a living, effective part of your daily operations. By meticulously organizing your documentation for both design (Type 1) and operational effectiveness (Type 2), you provide your auditor with a clear, defensible narrative of resilience that is essential for a successful audit report.