A SOC 2 Type 2 audit is an independent CPA examination that evaluates whether a service organization’s controls were suitably designed and operated effectively over a defined review period, commonly 6 to 12 months (Secureframe). The counterintuitive part is that many first-time buyers focus on the audit itself when the actual business decision is everything around it: scope, auditor choice, readiness work, and evidence discipline. Those choices determine whether the report helps sales, drags leadership time into remediation, or becomes an expensive document that still doesn’t satisfy customer scrutiny.
For a CTO or founder, this matters because a soc 2 type 2 audit is rarely just a compliance project. It affects procurement reviews, security questionnaires, contract cycles, and the confidence enterprise buyers place in your operating discipline. If you handle customer data in AWS, Azure, or both, your control design also needs to reflect the realities of cloud operations. Teams building that foundation often benefit from practical guidance on securing AWS and Azure environments, especially before evidence collection starts.
What a SOC 2 Type 2 Audit Is
A SOC 2 Type 2 audit is the report buyers ask for when they want proof your controls held up in day-to-day operations, not just on paper. A licensed CPA firm examines whether the controls tied to the selected Trust Services Criteria were designed appropriately and operated effectively over a defined review period.
That point changes how a first-time team should plan the work. The audit is not a policy writing exercise. It is a sustained evidence exercise. Auditors will expect to see that access reviews happened on schedule, change approvals were documented, incidents were tracked, vendor due diligence was performed, and exceptions were handled consistently across the period under review.
Why founders and CTOs should care
For many SaaS, FinTech, and HealthTech companies, SOC 2 Type 2 becomes a sales requirement before it feels like an internal priority. Enterprise buyers often stop accepting long security questionnaires as a substitute for independent assurance. A clean report gives procurement, legal, and security reviewers a standardized package. That usually shortens review cycles and reduces the number of custom follow-up requests your team has to answer live.
The market is also pushing toward broader and heavier reports. CBIZ noted that SOC 2 reports with more than 150 security controls increased from 16% in 2023 to 23% in 2024. The same study found that 9.6% of SOC 2 reports used a multi-framework “SOC 2+” format, as reported in the 2024 CBIZ benchmark findings. The practical takeaway is simple. Buyers are getting used to seeing more mature control environments, but adding controls without a clear reason creates more testing, more screenshots, and more leadership time spent on audit support.
For a CTO or founder, a soc 2 type 2 audit is rarely just a compliance project because it influences sales velocity, customer confidence, and the amount of engineering time diverted into remediation. If your environment spans multiple cloud providers, control design also has to reflect that operational reality. Teams preparing for evidence collection often benefit from practical guidance on securing AWS and Azure environments.
Practical rule: A SOC 2 Type 2 report helps the business only when the scope matches what customers actually ask you to prove.
What the report is really testing
A first-time buyer should evaluate the audit in three parts.
-
Your system description
This defines what is actually in scope, including products, infrastructure, people, processes, and subprocessors. If important services are excluded, the report may not satisfy customer reviewers. -
Your control set
This is the collection of policies, procedures, technical safeguards, and recurring review activities mapped to the Trust Services Criteria you selected. -
Your operating evidence It is often during this phase that many first audits get expensive. Auditors ask for dated artifacts such as logs, tickets, approvals, review records, training completion, risk assessments, and incident documentation from the observation period.
A clean opinion tells a buyer that your security program is repeatable and managed, not dependent on a few individuals remembering the right steps at the right time. That is why the scoping decision, the evidence model, and the auditor you choose have direct business consequences long before the final report is issued.
SOC 2 Type 2 vs Type 1 Explained
Choosing the wrong report wastes time twice. For a first-time buyer, the key decision is whether you need a design opinion now or operating assurance that will hold up in enterprise security review.
A Type 1 report assesses whether controls are designed appropriately at a specific date. A Type 2 report assesses whether those controls operated effectively over a review period, usually several months. Buyers read those reports differently. A procurement team may accept Type 1 as an interim step. A mature security team usually wants Type 2 because it shows the process worked in practice, not just on paper.
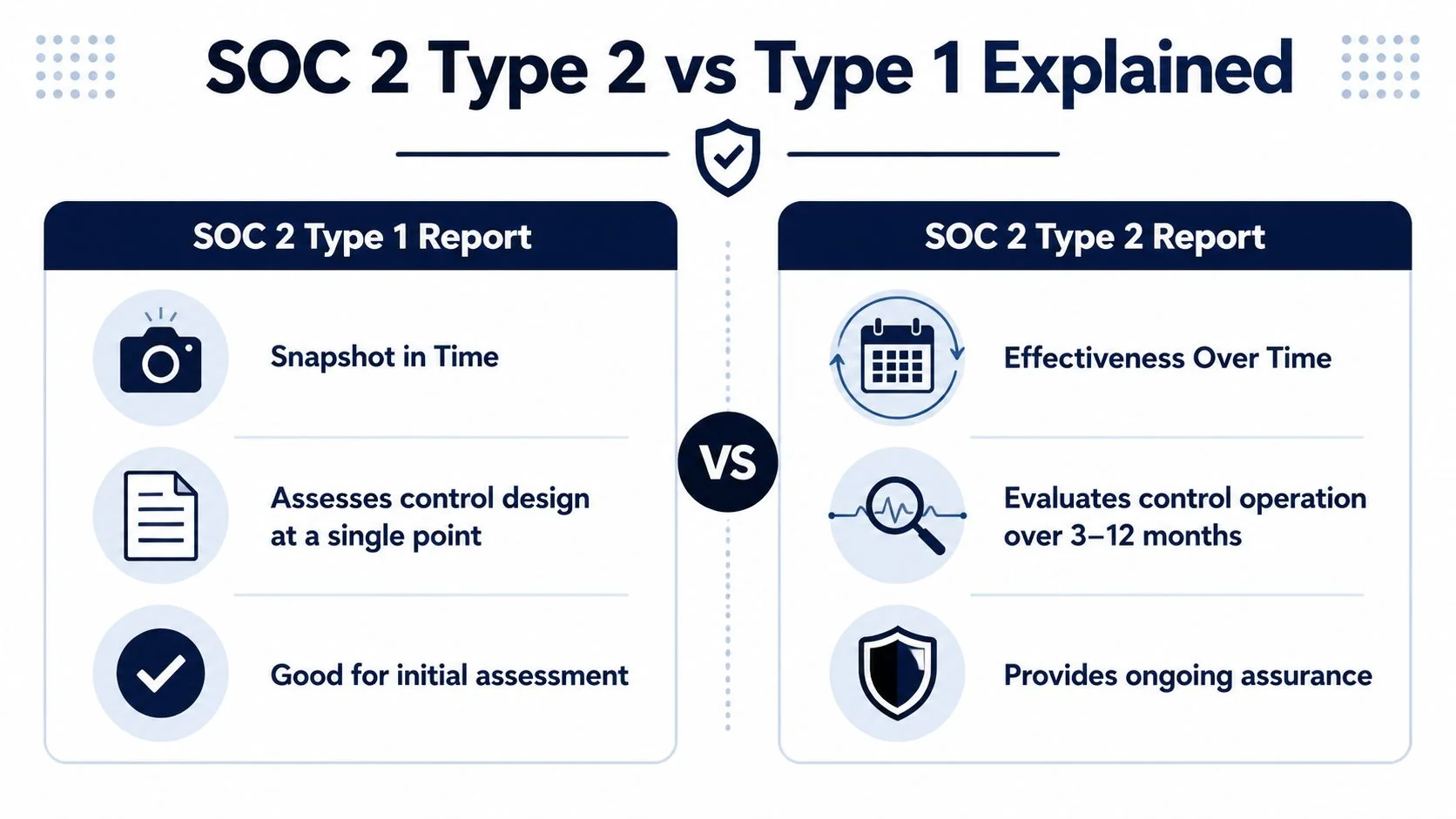
The practical trade-off
Type 1 is faster to get. Type 2 carries more sales value.
That trade-off affects budget, timing, and how much internal discipline your team needs before fieldwork starts. With Type 1, the auditor can confirm that access reviews, change approvals, and incident procedures are defined and mapped correctly. With Type 2, the auditor tests whether those activities occurred, whether they happened on schedule, and whether the evidence is complete enough to support an opinion.
Here is the decision in plain terms:
| Report type | Best fit | Main limitation |
|---|---|---|
| SOC 2 Type 1 | Early-stage company that needs a near-term attestation for deals already in motion | Shows control design at a point in time, not sustained execution |
| SOC 2 Type 2 | Company selling into mid-market or enterprise accounts that expect proof over time | Requires months of evidence collection, tighter process ownership, and more audit effort |
For teams still finalizing scope, this overview of the SOC 2 Trust Services Criteria and how they shape report expectations helps clarify what buyers will see in either report type.
What auditors do differently in Type 2
In a soc 2 type 2 audit, auditors test operation, not intent. A policy alone is not enough. They sample tickets, approvals, logs, access reviews, training records, and incident documentation across the review period to confirm the control worked consistently.
That is where first audits often get exposed.
Common failure points include:
- Access reviews defined in policy but missing dated evidence
- Engineering approvals handled in Slack or verbally instead of in Jira or GitHub
- Vendor reviews assigned annually but never completed
- Monitoring alerts generated without documented triage or resolution
Those gaps are not academic. They drive exceptions, delay report issuance, and create extra work for engineering, IT, and compliance at the worst possible time.
If evidence lives in screenshots, DMs, and someone’s memory, Type 2 fieldwork will be slow and expensive.
Which one should a first-time buyer choose
Choose Type 1 if you need a credible bridge document for current deals and your target customers will accept it. Choose Type 2 if enterprise buyers are already asking how long controls have been in place, whether reviews recur on schedule, and whether anyone independently tested execution.
I usually advise founders to decide based on revenue motion, not anxiety. If the sales team is hearing, “Send the SOC 2 when ready,” Type 1 can buy time. If the sales team is hearing, “We require Type 2 before signature,” starting with Type 1 often adds cost without solving the actual blocker.
The expensive mistake is treating Type 1 as the default first step. It only works when it matches buyer expectations and gives the team enough time to build repeatable evidence before the Type 2 period begins.
Decoding the Five Trust Services Criteria
The wrong Trust Services Criteria scope creates two expensive problems. You either pay for controls and testing customers did not ask for, or you finish the audit and still lose deals because the report misses the risk areas buyers care about.
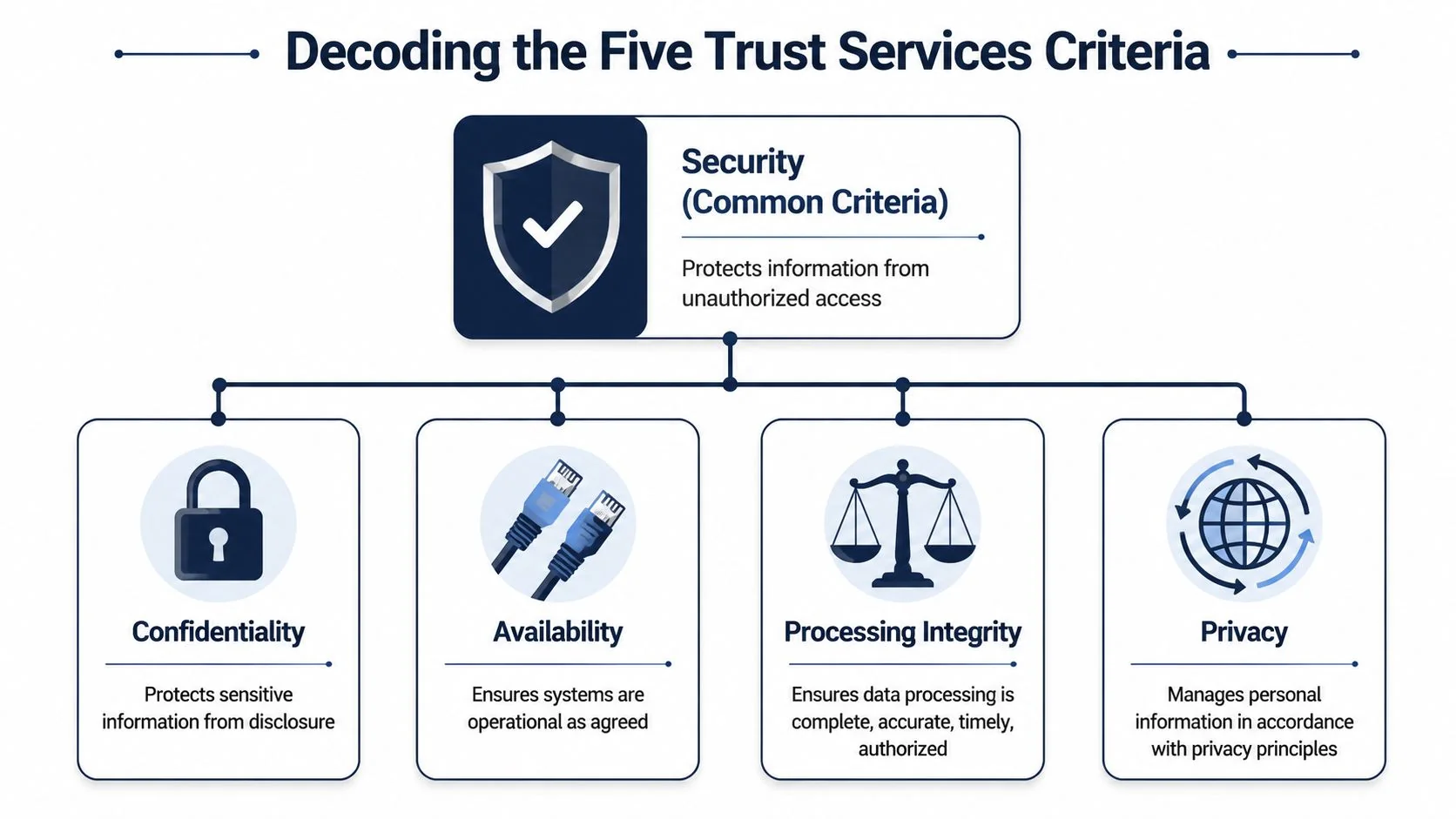
Every SOC 2 report includes Security. The other four criteria are elective. In practice, the decision should come from your product, your contracts, and the questions showing up in security reviews.
Security is the base layer
Security, often mapped to the Common Criteria, covers the controls auditors expect to see in nearly every first-time SOC 2: access management, risk assessment, logging and monitoring, change management, incident response, vendor oversight, and governance.
For a SaaS company, that usually means control evidence around:
- access provisioning and deprovisioning
- MFA and authentication controls
- vulnerability management
- logging and monitoring
- change approval workflows
- incident response procedures
If your team is still cleaning up those basics, adding more criteria usually increases audit hours and remediation work without improving the report’s sales value. A useful reference before finalizing scope is this overview of the SOC 2 Trust Services Criteria.
The four optional criteria and when they earn their place
Availability
Choose the Availability criterion when your customer promise includes uptime, resilience, backups, disaster recovery, or service continuity. If MSAs, order forms, or security questionnaires ask about restoration targets, downtime handling, or production monitoring, this criterion often belongs in scope.
Availability is one of the most common add-ons to Security. For first-time buyers, that usually signals a practical point: if customers depend on your service to stay online, auditors and prospects will expect to see more than generic security controls.
Confidentiality
Confidentiality fits products that store or handle sensitive business information that is not public and should only be accessed by authorized users. That can include uploaded files, customer exports, financial data, internal models, support attachments, or contract-restricted datasets.
This criterion is often the right choice for B2B SaaS teams selling into legal, finance, healthcare, or enterprise IT buyers. Those customers may care less about privacy-specific obligations and more about whether proprietary information stays contained.
Processing Integrity
Processing Integrity applies when the product’s value depends on correct system output. Billing platforms, workflow engines, data sync tools, and transaction products often land here because customers need confidence that the system processes data completely, accurately, on time, and with proper authorization.
This is the criterion teams add too casually. If your product is mostly a system of record or collaboration layer, buyers may not expect Processing Integrity. If your platform calculates payroll, routes payments, pushes security alerts, or triggers operational workflows, they often will.
Privacy
Privacy is narrower than many founders assume. It focuses on how personal information is collected, used, retained, disclosed, and disposed of under stated privacy commitments.
A company can have strong security controls and still have no reason to include Privacy in SOC 2 scope. Add it when the business makes explicit privacy commitments, handles regulated personal data in a way customers examine closely, or needs the report to answer recurring privacy diligence from larger buyers.
How to scope without overspending
A first audit usually comes down to three questions:
- What does the product do?
- What are customers, prospects, and contracts asking you to prove?
- Can the team run the added controls cleanly for the full audit period?
That last question gets missed. Every added criterion expands testing, evidence collection, and the number of ways fieldwork can stall.
A practical rule is simple. Scope to revenue and system risk, not to aspiration. If enterprise prospects keep asking about uptime commitments, Availability can shorten security review cycles. If no buyer has asked about Privacy and your data practices do not create that obligation, leave it out until there is a business reason to include it.
Over-scoping increases cost, stretches internal owners, and raises the odds of exceptions. Under-scoping pushes the problem into sales, where each missing criterion turns into extra questionnaires, calls with security teams, or a delayed signature.
The End-to-End SOC 2 Type 2 Timeline
A first SOC 2 Type 2 usually takes longer than the buyer expects, the founder hopes, and the sales team promised. The teams that stay on schedule are the ones that choose an auditor early, scope tightly, and build the project around a real customer deadline instead of an optimistic target.
Phase 1 and Phase 2
The calendar starts well before the observation window.
Scoping and readiness
This phase sets the cost and the failure rate for everything that follows. The company defines the in-scope system, confirms which Trust Services Criteria will be tested, identifies control owners, and checks whether each control leaves evidence an auditor can inspect.
That last point drives more delays than founders expect. A control can exist in practice and still fail audit testing if nobody can show dated approvals, access reviews, onboarding records, incident logs, or change tickets. If engineering approves production changes in Slack and HR handles offboarding through ad hoc messages, fix that before the audit period begins.
Auditor selection belongs here too, not at the end. A specialist firm may move faster and give more hands-on guidance. A larger firm may carry more brand recognition with enterprise buyers but often brings a higher fee and a more rigid process. For a first-time buyer, the right question is not “Who is the most prestigious?” It is “Who can audit our scope on our timeline, and what will our customers care about?”
Remediation
Readiness always surfaces gaps. Teams usually need to formalize vendor review, tighten MFA enforcement, document risk assessment cadence, clean up joiner-mover-leaver workflows, or make sure systems like Jira, Okta, GitHub, Google Workspace, AWS, Azure, Vanta, or Drata retain usable evidence.
This work can move fast if ownership is clear. It drags when every control depends on a different team and nobody has authority to force a deadline.
Phase 3
The observation period is where companies either build a clean report or collect exceptions. Controls have to operate consistently for the full review window, not just during the final few weeks.
For planning, assume months of operating history plus a shorter fieldwork period at the end. Some companies choose a shorter observation window for the first report. Others run longer to match customer expectations or reduce questions about limited history. The trade-off is simple. A shorter window can get a report into market faster, but it gives the auditor less operating history to test and may invite more diligence questions from larger prospects.
This is why reverse-planning matters. If a major prospect says “send the SOC 2 by Q4,” the company needs to count backward from report issuance, not from audit kickoff. Time is lost in contracting with the CPA firm, cleaning up evidence collection, and waiting on internal teams that still have day jobs.
You can compress remediation with enough focus. You cannot compress control history once the clock has started.
Phase 4 and report issuance
Fieldwork is the part external teams see, but by then the outcome is mostly set. Auditors request samples, walkthroughs, policy support, screenshots, exports, and explanations for how each control operated during the period. If evidence is organized and owners respond quickly, fieldwork feels manageable. If artifacts live across inboxes, tickets, shared drives, and personal notes, the process turns into expensive reconstruction work.
This is also where auditor quality shows up. A good auditor runs a disciplined request list, explains what will satisfy testing, and avoids forcing the client to guess. A poor fit creates churn, repeats requests, and burns engineering time. That matters because the internal cost of fieldwork often exceeds the pain of the audit fee itself.
Later in the process, this walkthrough helps non-GRC stakeholders understand what fieldwork will feel like:
A realistic planning model
Use this sequence to plan against revenue targets and procurement dates:
| Phase | What matters most |
|---|---|
| Scoping | Define the system honestly and confirm what customers will expect to see in scope. |
| Auditor selection | Compare firms on timeline, audit approach, responsiveness, and buyer credibility, not just logo recognition. |
| Readiness and remediation | Fix control design and evidence capture before the observation window starts. |
| Observation period | Run controls on schedule and document them as they happen. |
| Fieldwork | Answer requests quickly with dated, traceable evidence. |
| Final report | Review the system description, exceptions, and presentation carefully before issuance. |
A practical first-cycle plan also assumes the renewal starts soon after the first report lands. Reports age quickly in enterprise sales. The best first audit is not the one that barely gets done. It is the one that gives the team a repeatable operating model for the next cycle.
Budgeting for Your SOC 2 Type 2 Audit Costs
Budgeting for a SOC 2 Type 2 audit goes wrong when the team treats the CPA quote as the whole project. It rarely is. The audit fee is only one line item in a larger decision about scope, internal labor, tooling, and how fast you need a report in customers’ hands.
For first-time buyers, the practical question is not “What does a SOC 2 cost?” It is “What scope do we need, and what will it take to operate those controls for a full period without slowing the business down?” That framing usually saves more money than haggling over a few thousand dollars in audit fees.
The budget has four parts
A workable budget usually includes these buckets:
-
Audit fee
The CPA firm’s fee for the examination, testing, and final report. -
Readiness support
Internal GRC effort or outside help to map controls, close design gaps, and organize evidence before fieldwork starts. Teams that need extra implementation support often use outside specialists or Hire CPAs to expand accounting and compliance capacity. -
Automation tooling
Platforms such as Vanta or Drata can reduce evidence collection work, but they do not fix weak process. If access reviews are late or change approvals are inconsistent, the tool will expose that faster. It will not solve it for you. -
Internal labor
This is the line item founders miss. Engineering supports change management evidence. IT handles access and device controls. HR provides onboarding and termination records. Leadership approves policies, exceptions, and risk decisions.
What actually drives cost
The biggest cost driver is scope. Every extra Trust Services Criteria category, in-scope system, subsidiary, or manual control increases testing volume and review time.
| Cost Factor | Lower-cost scenario | Higher-cost scenario |
|---|---|---|
| Trust Services Criteria | Security only | Security plus multiple optional criteria |
| Environment complexity | Limited stack, clear boundaries | Many integrations, multiple environments, several subprocessors |
| Employee count | Smaller team, fewer access changes | Larger team, more joiners, movers, and leavers |
| Evidence collection | Centralized records, repeatable exports | Manual screenshots, scattered artifacts |
| Control maturity | Owners know the cadence and keep records | New controls, missed reviews, remediation during the period |
The trade-off is straightforward. A narrower scope costs less and moves faster, but it only works if it matches buyer expectations. If enterprise prospects expect availability or confidentiality in scope, a cheaper security-only report may still create sales friction.
Where first-time teams overspend
The first mistake is paying for scope they do not need. I see this often with startups that add criteria because they sound prudent, then discover buyers only asked for Security. Extra criteria can be justified, but they should map to a sales requirement, contractual need, or real risk in the product.
The second mistake is underfunding evidence operations. A control that exists on paper but is performed inconsistently creates rework, exceptions, and more auditor questions. That cost lands on engineering and operations, not just the compliance budget.
The third mistake is choosing vendors in isolation. Tooling, readiness support, and the auditor should fit the same operating model. If you want a practical way to evaluate firms before you lock the budget, review this guide to Big Four vs specialist SOC 2 auditors.
A budgeting lens that holds up
Use two filters before approving spend:
- What will customers and procurement teams require in the next 12 months?
- What controls can this team run on schedule every quarter without heroics?
That is the difference between a one-time compliance project and a report that supports sales year after year.
Choosing Your Auditor Big Four vs Specialist Firms
Auditor selection is where many first-time buyers lose time and money. The logo on the proposal matters less than fit: industry familiarity, responsiveness, clarity during scoping, and how well the firm handles first-cycle companies.
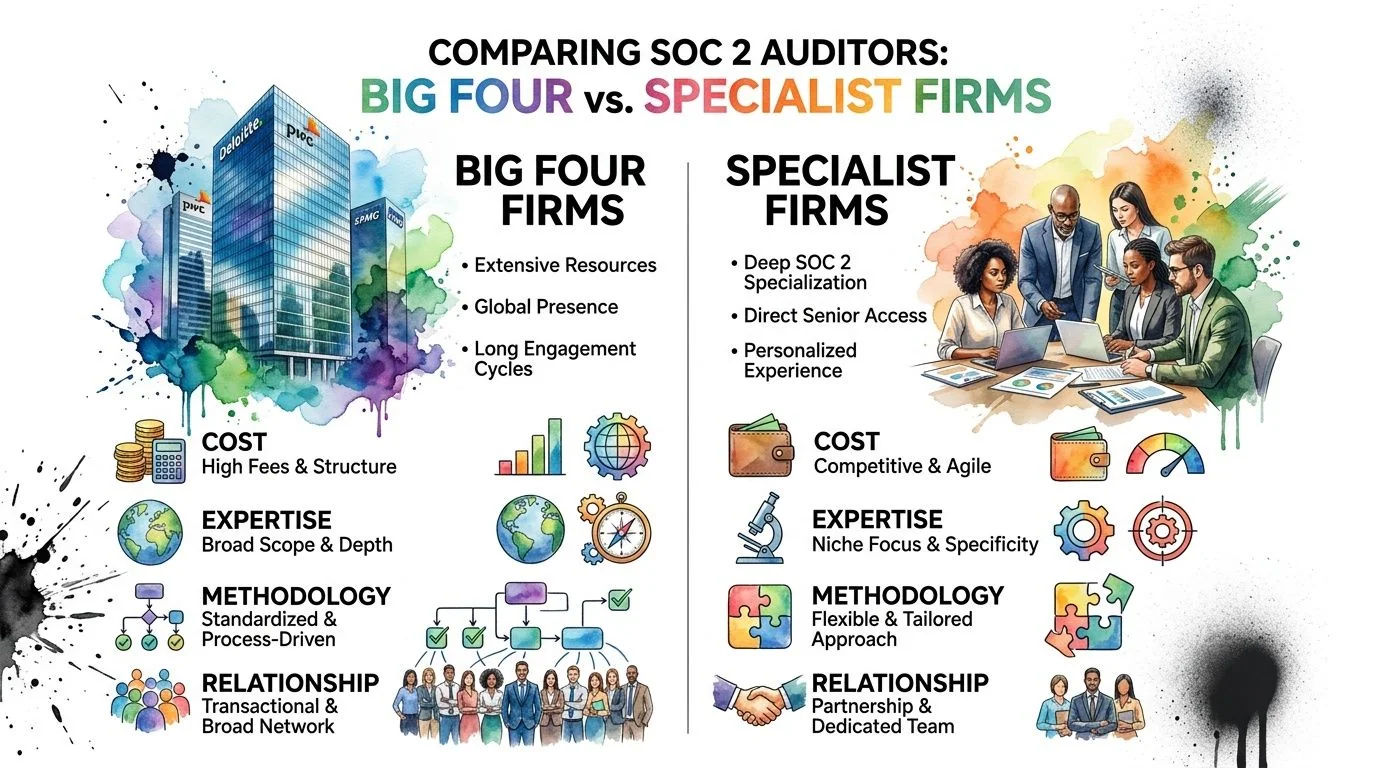
The market spread is wide
NordLayer’s review of SOC 2 Type 2 pricing cites data from 90+ verified auditors showing that specialist boutique firms charge $15K to $80K with 3 to 6 month timelines, while Big Four firms can cost $200K to $400K+ and take 12 to 20 months. The same data highlights potential 30 to 50% cost overruns for first-time buyers who don’t compare options carefully.
That should change how you shop. “We need a well-known name” is not a strategy. It’s a preference that may or may not match your stage, budget, or sales motion.
How to choose based on business context
Use this lens instead of defaulting to prestige:
| Auditor type | Usually best for | Watch-outs |
|---|---|---|
| Specialist SOC firms | Startups and mid-market teams that need speed, practical guidance, and tighter budgets | Quality varies. You need to vet responsiveness and first-cycle experience. |
| Big Four | Companies with complex stakeholder expectations, broader assurance relationships, or specific brand requirements | Higher cost, longer timelines, and often less flexibility for smaller clients. |
A specialist firm often works well when your environment is cloud-native, your internal team is lean, and you need direct answers during readiness and fieldwork. Big Four firms can make sense if your board, customers, or transaction context specifically value that brand.
If you need a structured process for comparing credentials and fit, this guide on Big Four vs specialist SOC 2 auditors is a helpful starting point. Some finance leaders also use external directories such as Hire CPAs to widen the initial search before narrowing to firms with actual SOC 2 depth.
Questions to ask before signing
Don’t just ask for a proposal. Ask for operating clarity.
- How many first-time SOC 2 Type 2 clients do you handle each year?
- What does your request list typically look like during fieldwork?
- How do you handle scoping disagreements early?
- Who runs day-to-day communication once the engagement starts?
- How much of the process is standardized versus partner-dependent?
The right auditor should reduce ambiguity. If the sales process already feels vague, the audit probably will too.
A Practical Checklist for Audit Readiness and Avoiding Pitfalls
The fastest way to make a soc 2 type 2 audit slower is to skip readiness work. Pre-audit gap assessments are not optional hygiene for first-time teams. They are one of the most impactful decisions in the process.
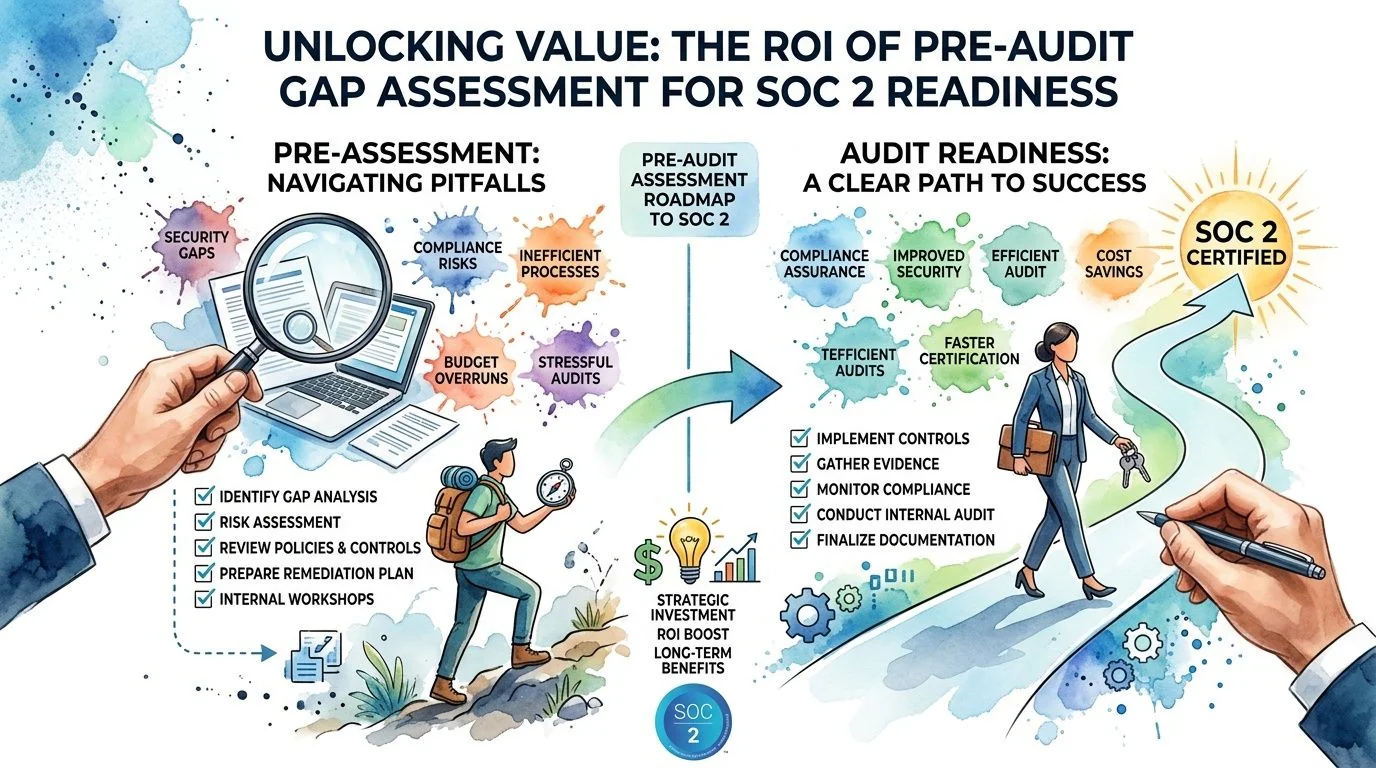
According to IS Partners’ analysis of SOC 2 gap assessments, pre-audit gap assessments can reduce audit exceptions by 40 to 60%, cut remediation time by 3 to 6 months, and improve the rate of an unqualified opinion to 85% compared with 60% for firms that skip them. For someone pursuing SOC 2, that’s the clearest ROI in the entire project.
A readiness checklist that actually helps
Use this as an operating checklist, not a document checklist.
-
Lock the scope
Define the in-scope product, environments, teams, and subprocessors. Don’t let this drift mid-period unless there’s a compelling business reason. -
Assign control owners
Every key control needs a named owner in engineering, IT, HR, security, or operations. Shared ownership usually means no ownership. -
Make evidence collection repeatable
Pull approvals from Jira, change evidence from GitHub, access reviews from Okta or your IAM tool, and monitoring artifacts from your SIEM or alerting stack. If evidence lives only in screenshots, fix that. -
Review policies against practice
Your access control, incident response, change management, vendor management, and risk assessment policies should match what teams practice. -
Test exception handling
Auditors know real environments have mistakes. What matters is whether you detect them, record them, remediate them, and show the trail. -
Organize institutional knowledge
Evidence gets delayed when only one person knows where things live. A simple internal documentation discipline helps a lot. Teams often benefit from stronger documentation habits such as effective knowledge base management for startups, especially when onboarding new control owners.
A clean report usually comes from boring consistency. Not heroic last-minute effort.
Pitfalls that derail first audits
Some failures are predictable.
-
Undefined system boundaries
Customers read the system description closely. If it’s vague, they ask more questions. -
Informal approvals
Slack messages and verbal sign-offs don’t make strong audit evidence. -
Weak vendor management
If critical vendors handle sensitive data, their due diligence needs to be documented and current. -
Late ownership decisions
When control ownership gets assigned during fieldwork, evidence quality drops fast. -
Tool-first thinking
Vanta or Drata can help. They cannot replace an actual process.
The strongest readiness posture is one where controls are part of normal operations, not a parallel compliance ritual. That’s the core connection back to SOC 2 audit readiness. If your team can scope cleanly, choose the right auditor, collect evidence continuously, and fix gaps before fieldwork, a soc 2 type 2 audit becomes much more than a report. It becomes a reliable proof point that your company is ready for customer diligence, annual renewals, and the next stage of enterprise growth.
If you’re comparing firms for your first report, SOC2Auditors helps you evaluate auditor options using verified pricing, timelines, and fit criteria so you can approach SOC 2 audit readiness with clearer expectations and fewer surprises.