A Service Organization Control (SOC) 2 report and a SOC 3 report are both attestations performed by a licensed CPA firm in accordance with standards set by the American Institute of Certified Public Accountants (AICPA). A SOC 2 report provides a detailed description of a service organization’s system and the design (Type 1) or design and operating effectiveness (Type 2) of its controls relevant to the AICPA’s Trust Services Criteria. A SOC 3 report provides the auditor’s opinion on whether the entity maintained effective controls over its system, also based on the Trust Services Criteria, but does not include the detailed system description or the specific tests of controls and their results.
Understanding SOC 2 and SOC 3 Reports
A SOC 2 report is a confidential, restricted-use document designed for knowledgeable stakeholders such as customers, partners, and regulators who require a deep understanding of a service organization’s internal control environment. It provides a detailed system description, management’s assertion, the auditor’s opinion, and a comprehensive section detailing the auditor’s tests of controls and the results of those tests. This granular level of detail is essential for formal vendor risk assessments and due diligence processes.
In contrast, a SOC 3 report is a general-use, publicly shareable document derived from the same audit procedures as a SOC 2. It contains the auditor’s opinion on the effectiveness of the controls but omits the sensitive, detailed information about the system description, specific controls, test procedures, and test results. It serves as a public-facing attestation of compliance, often accompanied by a seal for marketing purposes.

Core Structural Differences
For an organization pursuing SOC 2 compliance, the structural differences between the reports dictate how audit results can be communicated to different audiences, impacting sales, marketing, and partnership agreements.
A SOC 2 report is a long-form document, often 50-100+ pages, containing proprietary details about your system and controls. This includes specific control language aligned with AICPA Trust Services Criteria like CC6.1, which requires the organization to “identify, select, and develop control activities.” The report would describe these activities and the auditor’s tests to validate them.
A SOC 3 report is a condensed summary, typically 10-20 pages. It provides the auditor’s opinion but strips out the detailed control matrix and test results, making it suitable for public distribution without exposing sensitive operational data.
Why does this matter for someone pursuing SOC 2? The choice of report deliverable is a strategic decision made during the audit planning phase. If your target customers are enterprise clients who conduct rigorous vendor due diligence, a SOC 2 is mandatory. A SOC 3 is a supplementary marketing tool. You must align your audit deliverable with the assurance requirements of your key stakeholders.
Practical Implications for Your Business
The decision between a SOC 2 and a SOC 3 report has direct, actionable consequences for your operations and go-to-market strategy.
| Feature | SOC 2 Report | SOC 3 Report |
|---|---|---|
| Intended Audience | Customers, partners, and auditors under a Non-Disclosure Agreement (NDA). | The general public, prospects, and website visitors. |
| Level of Detail | Extremely high; includes specific control descriptions, auditor’s test procedures, and results. | High-level summary; provides the auditor’s opinion but omits detailed test information. |
| Distribution | Restricted use; requires an NDA to share, protecting sensitive operational information. | General use; can be freely distributed and published on your website. |
| Primary Use Case | Vendor due diligence, contractual compliance, and in-depth risk assessments. | Marketing, sales enablement, and building broad public trust. |
Why does this matter for someone pursuing SOC 2? Understanding these differences is fundamental to your compliance journey. If you only obtain a SOC 3, you cannot satisfy enterprise customers who require the detailed control evidence found only in a SOC 2. Conversely, relying solely on a SOC 2 limits your ability to market your security posture broadly. This decision, made early in the process as you prepare for your SOC 2 audit, dictates your budget, timeline, and the ultimate utility of your audit investment.
A Deep Dive into Report Content and Assurance Levels
The core audit process for both a SOC 2 and a SOC 3 report is identical; the difference lies exclusively in the content and presentation of the final report. The level of assurance provided by the auditor is the same for both, but the level of transparency offered to the reader is fundamentally different.
A SOC 2 report contains four critical sections: Management’s Assertion, the Auditor’s Opinion, a detailed System Description, and the detailed matrix of controls, the auditor’s tests, and their results. This provides the evidence needed for a third party to perform their own risk analysis.
A SOC 3 report contains Management’s Assertion and the Auditor’s Opinion but omits the detailed System Description and the exhaustive control testing matrix. It attests to compliance without revealing the underlying operational details.
Why does this matter for someone pursuing SOC 2? You must implement and evidence controls to meet the AICPA Trust Services Criteria regardless of which report you ultimately issue. For example, to meet criterion CC7.2 (“The entity restricts logical access to information assets to authorized users”), you will need to demonstrate effective logical access controls. The SOC 2 report will detail how your controls work and how the auditor tested them. The SOC 3 will simply state that controls over logical access were effective, as part of the overall opinion. Your internal readiness efforts must produce the detailed evidence required for the SOC 2, even if you only plan to release a SOC 3.
The Anatomy of a SOC 2 Report
The value of a SOC 2 report lies in its detailed, evidence-based content, allowing stakeholders to validate your control environment against their specific risk tolerance.
The four key sections are:
- Management’s Assertion: A formal declaration from your organization’s management stating that the system is accurately described and the controls are suitably designed and (for a Type 2) operated effectively.
- Auditor’s Opinion: The CPA firm’s independent professional judgment on whether management’s assertion is fairly stated and if the controls meet the applicable Trust Services Criteria.
- System Description: A comprehensive narrative outlining the infrastructure, software, people, procedures, and data that constitute the service, providing context for the controls.
- Control Matrix and Test Results: The core of the report. This section lists each specific control, the auditor’s procedures to test that control, and the outcome of the tests. For example, a control for website password protection would be described here, along with the auditor’s test to confirm its enforcement.
The Streamlined Content of a SOC 3 Report
A SOC 3 report leverages the same underlying audit work as a SOC 2 but presents a condensed, public-friendly version. It provides the same level of auditor assurance but without the sensitive operational details.
Key Takeaway for SOC 2 Readiness: The fundamental difference is not the audit itself but the level of detail presented in the final deliverable. A SOC 3 report attests that you passed the examination; a SOC 2 report provides the evidence showing how you passed.
Because it lacks detailed test results, a SOC 3 is insufficient for most formal vendor risk management programs. Security-conscious enterprise customers need to review the specific controls and test results in a full SOC 2 audit report.
Why does this matter for someone pursuing SOC 2? Your go-to-market strategy must inform your audit strategy. If you target enterprise clients, planning for only a SOC 3 will result in a failed sales process. When a prospect’s security team requests your SOC 2 and you can only provide a SOC 3, the deal will stall. Aligning the report deliverable with market demand is a critical component of successful SOC 2 readiness.
Distribution and Confidentiality: A Strategic Choice
The rules governing the distribution of SOC 2 and SOC 3 reports are strict and are a primary driver in deciding which report to pursue. This is a strategic decision, not an administrative afterthought.
A SOC 2 report is a confidential, restricted-use document. Its distribution is contractually limited to specific parties—such as customers, business partners, and their auditors—who have a direct need to understand your internal controls and have signed a non-disclosure agreement (NDA).
Conversely, a SOC 3 report is a general-use, public-facing document. It is designed for broad distribution and can be posted on your company website, used in marketing materials, and shared freely without an NDA.

Why does this matter for someone pursuing SOC 2? How you handle the distribution of your SOC 2 report is itself a control activity that falls under the Confidentiality Trust Services Criterion. Your process for gating the report, requiring an NDA, and logging access must be robust and auditable. Mismanaging the distribution of a restricted-use report can lead to audit findings and potential breaches of confidentiality.
SOC 2: The Restricted Asset for Deep Due Diligence
The “restricted use” nature of a SOC 2 report is a critical feature that protects your organization’s sensitive operational information from public disclosure. Managing this asset requires a defined process:
- Implement a Gated Access Process: Require all requests for the SOC 2 report to go through a formal vetting process that includes the execution of a legally reviewed NDA.
- Use Digital Watermarking: Watermark each distributed copy with the recipient’s name and the date to discourage unauthorized sharing and aid in tracing any potential leaks.
- Maintain an Access Log: Keep a detailed, auditable log of every entity that has received your SOC 2 report, including the request date, recipient contact, and a record of the signed NDA. This log serves as evidence for your auditors.
Why does this matter for someone pursuing SOC 2? Your procedure for protecting and distributing the SOC 2 report itself can be examined by your auditor. This process directly supports the AICPA Trust Services Criterion C1.2, which addresses the protection of confidential information throughout its lifecycle, including its disposal. A weak distribution process undermines the very trust the report aims to build.
SOC 3: The Public-Facing Marketing Tool
The SOC 3 report is designed for maximum marketing impact, translating the successful outcome of your SOC 2 audit into a digestible format for a broad, non-technical audience.
Its primary function is to build trust at scale. For instance, a SaaS company can display a “SOC 3 Compliant” seal on its security page, with a direct link to the report PDF. This answers preliminary security questions for potential customers, shortens sales cycles for smaller clients, and serves as a powerful piece of marketing collateral.
Why does this matter for someone pursuing SOC 2? If your business model relies on a high volume of leads and a self-service or low-touch sales process, a SOC 3 can be a critical asset. It removes friction by proactively addressing security concerns, allowing your sales team to focus on feature and value discussions rather than initial security vetting. It demonstrates a commitment to security without the administrative burden of NDAs for every prospect.
Drilling Down on Cost and Timeline
A frequent misconception is that a SOC 3 audit is a cheaper, faster alternative to a SOC 2. This is incorrect. A SOC 3 report is an optional, supplementary deliverable generated from a full SOC 2 audit engagement. Therefore, the cost and timeline are primarily dictated by the underlying SOC 2 audit.
Why does this matter for someone pursuing SOC 2? Budgeting and project planning for your SOC 2 audit must account for the full scope of work, as there are no shortcuts. The decision to add a SOC 3 report is a marginal cost consideration, not a separate audit project. Understanding this allows for accurate financial planning and prevents unrealistic expectations about timelines.
How the Audit Costs Break Down
The majority of your investment is allocated to the SOC 2 audit itself, particularly a Type 2 engagement. This includes auditor fees for planning, fieldwork (testing controls, collecting evidence, interviewing personnel), and report writing.
The SOC 3 is an add-on deliverable. After completing the extensive SOC 2 audit, the CPA firm charges an additional fee to draft the summarized SOC 3 report.
Key Insight for SOC 2 Readiness: The core financial commitment is for the SOC 2 Type 2 audit. The SOC 3 is a relatively small incremental cost for generating a public-facing version of the results. You cannot purchase a SOC 3 engagement in isolation.
A comprehensive SOC 2 Type 2 audit typically costs between $25,000 and $400,000, with most mid-sized SaaS companies falling in the $30,000 to $75,000 range. The incremental cost for generating a SOC 3 report is usually an additional $5,000 to $15,000. CPA firms like Linford & Co offer detailed pricing guidance.
Mapping Out the Audit Timeline
The timeline for obtaining a SOC 3 report is entirely dependent on the completion of the SOC 2 audit. The most significant factor is the observation period required for a Type 2 report.
- Type 1 Report: A point-in-time audit of the design of your controls. The entire process, from readiness to final report, can often be completed in 2-4 months.
- Type 2 Report: An audit of the operating effectiveness of your controls over a period of time, typically six to twelve months. This observation period is the longest phase of the engagement.
After the observation period concludes, the auditor performs their final testing and report writing. Drafting the detailed SOC 2 report can take 4-6 weeks. If a SOC 3 report is also part of the engagement, it is drafted after the SOC 2 is finalized, typically adding another one to three weeks to the overall timeline.
Why does this matter for someone pursuing SOC 2? Project management is critical. If your marketing team plans a launch around the SOC 3 report, you must build the full SOC 2 Type 2 timeline (including the observation period and report writing) plus the extra drafting time for the SOC 3 into your project plan. Miscalculating this timeline can cause significant delays in your go-to-market initiatives. Proper SOC 2 audit readiness requires aligning your compliance roadmap with your business and marketing deadlines.
How Auditors Approach SOC 2 and SOC 3 Engagements
A critical point to understand is that auditors do not perform “SOC 3 audits.” They perform a single SOC 2 audit engagement based on the AICPA’s Trust Services Criteria. The SOC 3 report is an optional, alternative reporting format that summarizes the results of that single audit.
The audit fieldwork—including evidence requests, control testing, system walkthroughs, and personnel interviews—is identical whether the final deliverable is a SOC 2, a SOC 3, or both.
Why does this matter for someone pursuing SOC 2? This fact underscores that there are no shortcuts to compliance. Your internal controls must be designed, implemented, and operated effectively to withstand the full rigor of a SOC 2 audit to earn either report. Your readiness efforts must focus on building a robust, auditable control environment, as this is the foundation for both deliverables.
The Unified Audit Fieldwork
An auditor’s primary objective is to obtain sufficient, appropriate evidence to form an opinion on your control environment. This standardized process includes:
- Evidence Collection: Auditors request specific artifacts to prove controls are operating. For example, to test CC6.6 (related to change management), they will request a sample of change tickets, approvals, and testing documentation.
- Control Testing: Auditors select samples of transactions or events over the audit period to test control effectiveness. For a 12-month Type 2 audit, they might test a sample of employee terminations to ensure access was revoked in a timely manner, per your policy.
- Interviews and Walkthroughs: Auditors meet with control owners to confirm that documented procedures match actual practice. This verifies that controls are not just designed well but are also consistently followed.
The principles of evidence gathering in a SOC 2 audit are similar to those in a general cyber security audit, focusing on verifiable proof of control operation.
Shifting from Evidence to Narrative
The divergence in the auditor’s work occurs only in the final reporting phase, after all testing is complete.
For a SOC 2 report, the auditor compiles a detailed, restricted-use document. This involves meticulously describing your system, mapping controls to the Trust Services Criteria, and documenting their specific test procedures and results for each control.
Key Auditor Insight for SOC 2 Readiness: The SOC 3 report requires the auditor to translate complex audit results into a high-level, non-technical summary suitable for public consumption. They must provide their professional opinion on the effectiveness of your control environment without disclosing any of the sensitive operational details contained in the SOC 2.
For a SOC 3 report, the auditor’s task is to create a concise, general-use summary. They draft a report that includes their professional opinion and management’s assertion but deliberately omits the detailed system description and the control testing matrix. This requires skill to convey the assurance of a successful audit without revealing proprietary information.
Why does this matter for someone pursuing SOC 2? It reinforces that your internal readiness must be geared toward passing a full SOC 2 examination. Your team must focus on building a genuinely secure and well-documented program, knowing that the same level of scrutiny applies regardless of the final report format.
Making the Right Choice for Your Business
The decision to obtain a SOC 2 report, a SOC 3 report, or both is a strategic business decision, not merely a compliance task. The right choice is determined by your customer base, sales process, and marketing strategy. A well-planned reporting strategy transforms the audit from a cost center into a business enabler.
The central question to guide your decision is: “Whose assurance requirements must we satisfy?”
Why does this matter for someone pursuing SOC 2? Answering this question during your initial readiness assessment ensures that your audit engagement is scoped correctly from the outset. Choosing the wrong deliverable can mean wasting your audit investment on a report that doesn’t meet the needs of your most important customers, thereby failing to accelerate sales or reduce friction in the procurement process.
Scenario-Based Decision Making
Your business model and target market should dictate your reporting strategy.
-
B2B SaaS Selling to Enterprise: A SOC 2 Type 2 report is non-negotiable. Large organizations, particularly in regulated sectors like finance and healthcare, have mature vendor risk management programs that require the detailed control information found only in a SOC 2 report. Providing a SOC 3 will halt the sales process.
-
B2C or SMB-Focused Business: A SOC 3 report is a powerful marketing and sales tool. For customers without dedicated security teams, the SOC 3 serves as a credible, third-party validation of your security posture. It builds trust and can be a key differentiator without the friction of NDAs.
-
Hybrid Model (Selling to both SMBs and Enterprise): The optimal strategy is to obtain both reports. The SOC 3 can be published on your website for broad marketing and to satisfy smaller customers, while the SOC 2 is held in reserve for enterprise prospects who require it for their due diligence under an NDA.
Why does this matter for someone pursuing SOC 2? Aligning your report strategy with your sales motion directly impacts revenue. A SOC 2 unblocks enterprise deals, while a SOC 3 accelerates transactions with smaller clients. During SOC 2 readiness, map out your customer segments and their specific assurance needs to define your required audit deliverables.
This decision tree illustrates the process.
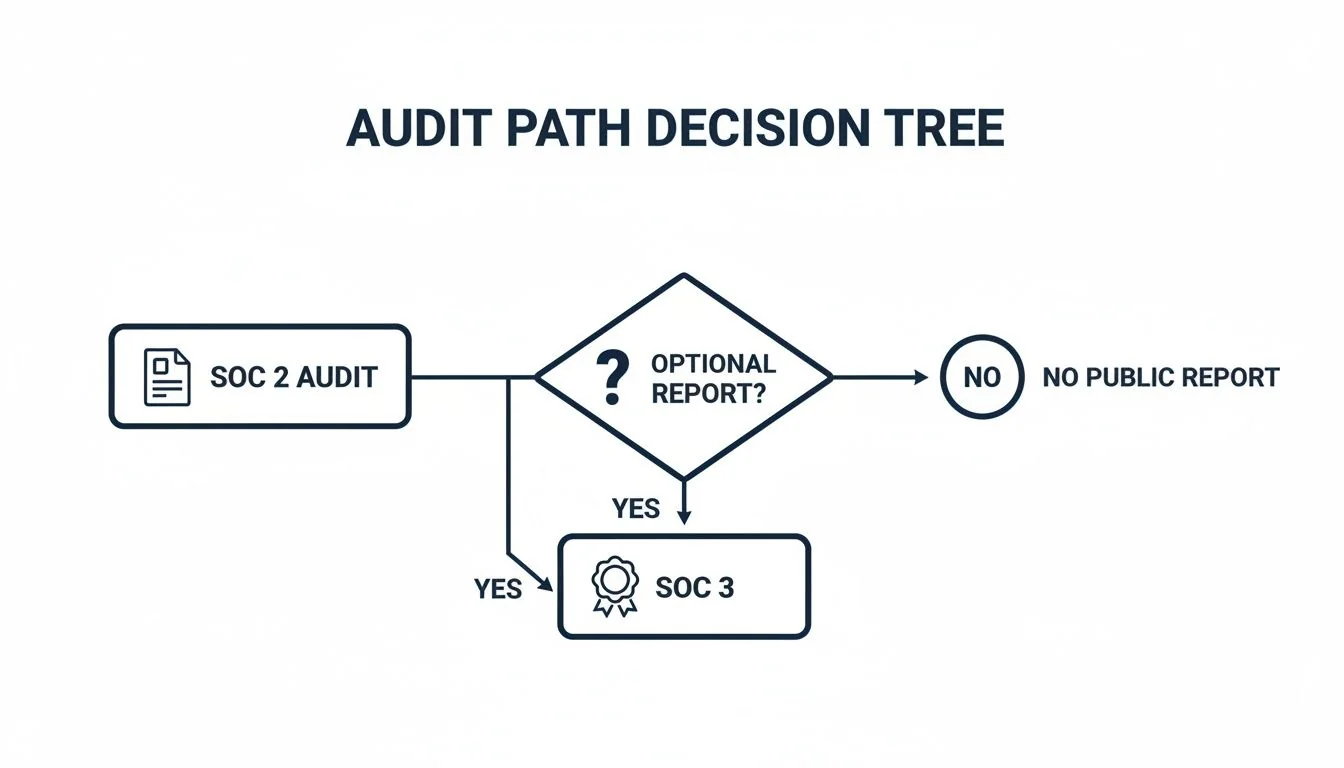
The key takeaway is that the SOC 3 report is an optional output of a primary SOC 2 audit, not a separate engagement.
Understanding the fundamental SOC 2 vs SOC 3 report differences is a cornerstone of effective SOC 2 audit readiness. By defining your audience and their assurance needs upfront, you ensure that your investment in the audit process yields a strategic asset that supports your business goals. This foresight transforms the audit from a compliance burden into a valuable tool for building trust, accelerating sales, and driving growth. Your readiness activities should not only focus on implementing controls but also on defining the strategic purpose and intended audience of the final report.
Navigating the complexities of selecting an auditor can be as challenging as the audit itself. At SOC2Auditors, we replace uncertainty with data-driven clarity. Compare 90+ verified audit firms by price, timeline, and industry expertise to find the perfect match for your business—without the sales calls. Find your ideal SOC 2 auditor with confidence.