SOC 2 employee security awareness training is a formal program designed to educate an organization’s personnel on their specific roles and responsibilities in protecting the security, availability, processing integrity, confidentiality, and privacy of customer data. It is a mandatory administrative control that organizations must implement to satisfy specific Trust Services Criteria (TSC) established by the American Institute of Certified Public Accountants (AICPA). The training program provides evidence to auditors that the entity has established a control environment to mitigate risks associated with human error and to ensure that all employees understand and can adhere to established information security policies.
The Role of Security Awareness in SOC 2 Compliance

For an organization pursuing SOC 2 compliance, a security awareness program is a critical internal control that auditors will directly test for both design and operating effectiveness. It is not merely a best practice; it is a foundational component of the control environment. The primary function of this training is to demonstrate to an auditor that the organization has systematically communicated security responsibilities to all personnel and has taken proactive steps to mitigate the risk of security incidents caused by human error.
From a compliance perspective, the program must be structured, ongoing, and, most importantly, provide auditable evidence of completion and comprehension. Why does this matter for someone pursuing SOC 2? Because auditors need to see that security is an embedded, operational discipline within the company culture, not just a set of policies in a binder. This is a direct requirement for building a defensible security posture and achieving a clean audit report.
Connecting Training to Trust Services Criteria
Your security awareness training program is not a standalone initiative; it directly satisfies and provides evidence for several AICPA Trust Services Criteria (TSC) that are central to a SOC 2 audit. Auditors will specifically map your training activities, documentation, and outcomes back to these criteria.
Here is how the training program provides evidence for specific SOC 2 requirements:
- CC1.2 (Control Environment): This criterion states, “The board of directors and management are responsible for their oversight responsibilities related to internal control.” A formal, mandatory training program serves as concrete evidence that leadership is fulfilling its oversight duties by ensuring all personnel understand their security obligations.
- CC2.2 (Communication and Information): This criterion requires the entity to communicate information to enable personnel to carry out their internal control responsibilities. Your training program is the primary mechanism for this communication, directly addressing the requirement by teaching employees about security policies, incident reporting procedures, and data handling rules.
For an auditor, a mature training program is tangible proof that an organization fosters a culture of security from the top down. It demonstrates that security is a shared responsibility and a managed control, which is essential for proving the effectiveness of your overall control environment.
In practice, your training program provides a key set of evidence. It tells a compelling story to your auditor: that you’re serious about protecting customer data and that your controls are operating effectively. To understand the full framework, review our complete guide on what SOC 2 compliance entails.
Ultimately, a strong security awareness program is your first and most important line of defense. It directly mitigates the risk of human error and gives auditors the concrete evidence they need that your controls are not only designed appropriately but are also operating effectively day-to-day. This shifts training from a simple HR task into a critical component of your audit readiness and risk management strategy.
Designing Your Audit-Ready Training Curriculum

When building your security awareness training for SOC 2, the curriculum must be designed to be directly auditable and aligned with the AICPA Trust Services Criteria. You’re creating a structured program that an auditor can map back to specific controls that mitigate identified risks.
Why does this matter for someone pursuing SOC 2? Because a generic, off-the-shelf program signals a “check-the-box” mentality. Auditors need to see that you have thoughtfully considered your organization’s specific risks and developed a curriculum to address them. This proves your commitment to CC1.2 (Control Environment) and CC2.2 (Communication) by showing that security is an integrated part of your operations.
The curriculum must start with a core set of topics applicable to every employee, establishing a consistent security baseline across the entire organization.
Core Curriculum for All Employees
Every employee, regardless of their role, interacts with company data and systems, making them a potential vector for a security incident. The foundational training must provide them with actionable guidance to perform their daily work securely.
The following topics are non-negotiable for all personnel:
- Phishing and Social Engineering: Provide specific training on how to identify suspicious emails, SMS messages (smishing), and voice calls (vishing). Use anonymized, real-world examples of attempts that have targeted your company to make the threat tangible. This directly addresses risks related to unauthorized access.
- Password and Credential Management: Enforce and explain the “why” behind your password policy (e.g., complexity, history, and rotation). Mandate and provide training on the use of multi-factor authentication (MFA). This is a critical control that auditors will test extensively.
- Secure Data Handling: Clearly define what constitutes sensitive data (e.g., PII, PHI, financial records) according to your data classification policy. Provide explicit rules for storing, transmitting, and securely deleting this data, including approved tools (e.g., sanctioned cloud storage) and prohibitions (e.g., use of personal devices or removable media).
- Incident Reporting: Establish a clear, step-by-step process for reporting a suspected security incident. Crucially, the policy and training must explicitly state there is no penalty for good-faith reporting. This encourages prompt reporting, which is vital for effective incident response and is a key element auditors look for.
The ROI for robust SOC 2 employee security awareness training is demonstrable. Consistent training strengthens key controls like password hygiene and threat identification, directly addressing AICPA criteria. For example, targeted sessions can reduce phishing risk by over 40% in just 90 days, while a comprehensive program can cut employee-driven security incidents by 72%. You can explore more about how training builds a secure workforce and impacts audit outcomes at MacPAS.com.
Tailoring Training for Specific Roles
A one-size-fits-all training curriculum is a red flag for a seasoned auditor. It indicates a lack of risk-based thinking. To demonstrate security maturity, you must provide specialized training tailored to the unique risks associated with specific job functions.
This is where your program proves its depth:
- Engineering and Development: This team requires specialized training on secure coding practices (e.g., OWASP Top 10), secure software development lifecycle (SDLC) processes, vulnerability management, and proper handling of secrets and credentials in code. Their training is a preventative control against application-level vulnerabilities.
- Sales and Marketing: This group handles large volumes of customer data, often on mobile devices and public networks. Their training must focus on the secure use of CRM systems, protecting data on laptops and mobile devices, and the risks of using untrusted Wi-Fi networks.
- Finance and HR: These departments are prime targets for attacks like business email compromise (BEC) and wire transfer fraud. Their curriculum must include deep dives into identifying and preventing such attacks, as well as the secure handling of sensitive personally identifiable information (PII) and financial data.
This role-based approach is crucial for SOC 2. It provides evidence that you have performed a risk assessment and implemented specific controls (in this case, targeted training) to mitigate those risks. By documenting both general and role-based training, you build a powerful evidence package that demonstrates a mature, risk-aware culture to your auditor.
Choosing Effective Delivery Methods and Frequency
From a SOC 2 auditor’s perspective, how you deliver security training is as important as what you teach. The delivery method and frequency are themselves part of the control.
Why does this matter for someone pursuing SOC 2? An auditor needs to see a structured, repeatable, and verifiable process. They are testing the operating effectiveness of your control, which means they need proof that every employee receives and understands the required information on a consistent schedule. Your delivery methods and cadence provide direct evidence that security is an ongoing operational process, not a one-time event, which is essential for satisfying criteria like CC1.2 (Control Environment).
There is no single “best” method, but certain approaches are far superior at generating the auditable evidence required for SOC 2.
Evaluating Training Delivery Methods
Your choice of delivery method directly impacts your ability to scale the program, engage employees, and produce audit-ready evidence. Here is a comparison of common methods through the lens of a SOC 2 audit:
- Learning Management Systems (LMS): An LMS is an automated software platform for deploying and tracking training. For SOC 2 evidence generation, this is the gold standard. It provides automated, time-stamped reports on course completion, quiz scores, and policy acknowledgments. This makes it simple to prove to an auditor that 100% of staff completed the required training.
- Live Instructor-Led Training (ILT): This includes real-time sessions, either in-person or via video conference. The primary benefit is high engagement and the ability to address role-specific questions. However, from an audit perspective, evidence generation is manual and more prone to error. You must meticulously track attendance via sign-in sheets or system logs and retain copies of the presentation materials for the audit period.
- Continuous Reinforcement: This is a critical supplementary method, not a primary one. It includes activities like simulated phishing campaigns, security newsletters, and brief security updates. This provides evidence to an auditor that security is a continuous process, which is vital for a Type 2 report that covers an extended period.
The most defensible approach for a SOC 2 audit is a blended model. Use a robust LMS for scalable, trackable core training for all employees. Supplement it with live, interactive sessions for high-risk roles and conduct continuous phishing simulations to test and reinforce the training’s effectiveness.
This table compares common training delivery methods on key factors relevant to SOC 2 compliance.
Comparing Security Awareness Training Delivery Methods
| Method | Scalability | Evidence Generation | Engagement Potential | Typical Cost |
|---|---|---|---|---|
| LMS Platform | High – Easily supports remote and growing teams. | Excellent – Automated reports, completion certificates, and quiz scores. | Medium – Can feel impersonal, but modern platforms use interactive elements. | $$ - $$$ |
| Live Training | Low – Difficult to scale across time zones and for new hires. | Fair – Requires manual tracking (attendance sheets, recordings). | High – Allows for real-time Q&A and role-specific discussion. | $ - $$$$ |
| Phishing Sims | High – Can be automated and sent to the entire organization easily. | Excellent – Provides clear metrics on click rates and reporting rates over time. | High – Directly engages users in a realistic, memorable way. | $ - $$ |
As you design your curriculum, remember that a great program has to cover how to handle security events. You can find excellent guidance on employee training on incident reporting and compliance to ensure your team knows exactly what to do when something goes wrong.
Establishing a Defensible Training Frequency
Your training schedule tells an auditor a story about your commitment to security. A sporadic, undocumented approach is a major red flag. For SOC 2, you need a predictable, documented cadence that covers every employee from day one.
A schedule that consistently passes SOC 2 audits follows this rhythm:
- Onboarding Training: All new hires must complete comprehensive security awareness training within their first 30 days of employment. This is a non-negotiable control to close the new hire vulnerability window. Evidence required: the signed offer letter acknowledging the policy and the LMS completion report with a date.
- Annual Refresher Training: Every employee, from the CEO to interns, must complete a full security training course at least once per year. This ensures that security knowledge remains current and addresses new threats or policy changes. Evidence required: an annual training report from the LMS demonstrating 100% completion.
- Ongoing Security Updates: Conduct quarterly or ad-hoc security updates to address emerging threats (e.g., a new widespread phishing campaign). Document these updates (e.g., copies of emails, Slack announcements) to show an auditor that your program is adaptive and proactive.
This multi-layered frequency is a cornerstone of a mature SOC 2 employee security awareness training program. It provides clear, consistent proof that you are not just designing controls but operating them effectively over time, which is the exact definition of what a SOC 2 Type 2 audit is designed to verify.
Documenting Training Evidence for Your SOC 2 Audit
Your SOC 2 employee security awareness training evidence is the collection of artifacts that proves to an auditor that your program exists, is active, and is effective. Without clear, organized, and verifiable evidence, your program is unauditable, which will result in a finding or exception in your report.
Why does this matter for someone pursuing SOC 2? Because the audit process is based entirely on evidence. An auditor cannot simply take your word that training occurred. They must be able to inspect tangible proof that your controls are designed appropriately and have been operating effectively throughout the audit period.
Your evidence must cover both the design of the program (e.g., policies, training materials) and its operating effectiveness (e.g., completion reports, phishing simulation results).
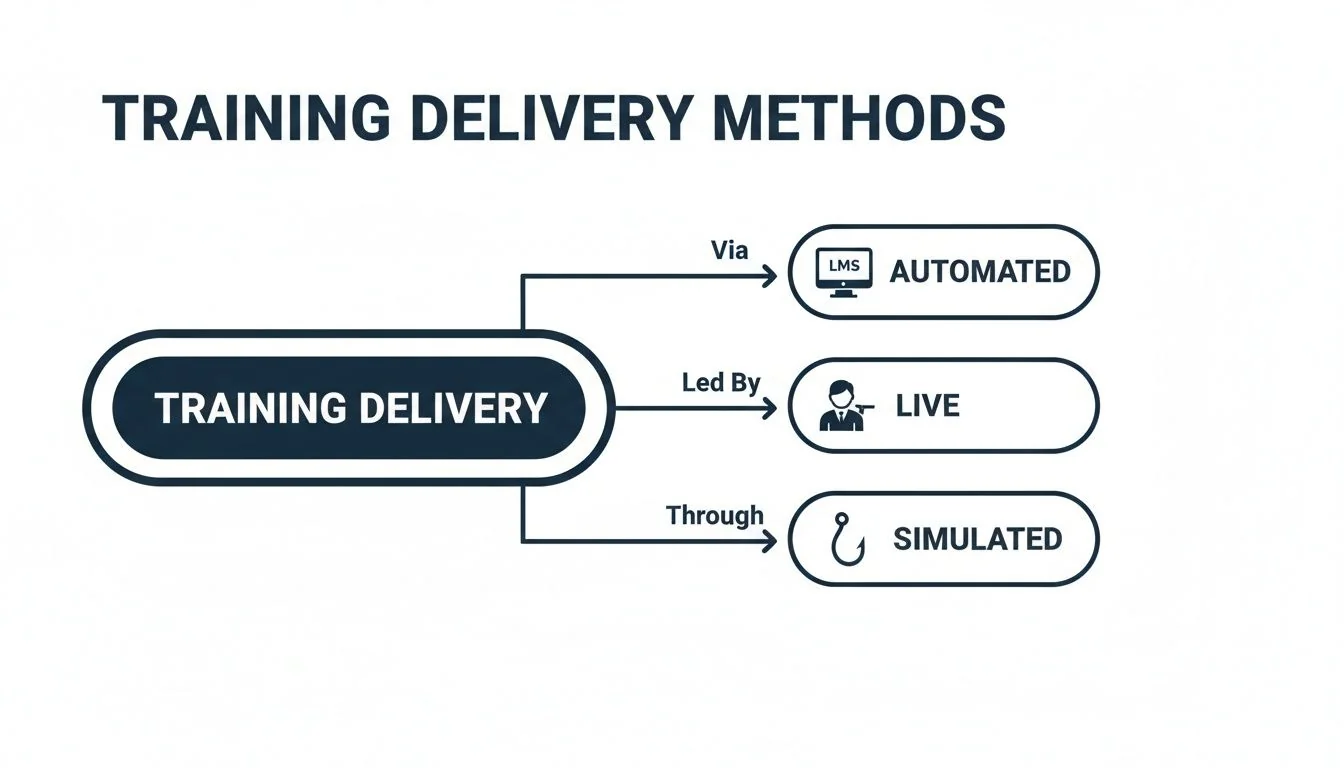
Each of these delivery methods—automated platforms, live instruction, and simulated phishing—generates its own distinct trail of audit evidence that must be collected and preserved.
Building Your SOC 2 Evidence Locker
An auditor’s request for evidence should be a simple retrieval task, not a frantic scramble. The key is to proactively collect and organize your evidence in a centralized repository, or “evidence locker.”
Here is the definitive checklist of artifacts every SOC 2 auditor will request for your training program:
- The Training Materials Themselves: A version-controlled copy of all slide decks, videos, and quiz questions used during the audit period. The auditor will review this content to ensure it is comprehensive and aligns with your stated security policies.
- Policy Acknowledgment Records: A record for every employee demonstrating that they have formally acknowledged receipt and understanding of the company’s information security policies. This is typically done via a signed form or a digital acceptance in an HRIS or LMS, captured upon hire.
- Completion Reports: This is the most critical piece of evidence. You need detailed reports from your LMS or manually compiled tracking sheets that list every employee’s name, their training completion date, and their quiz score. An auditor will sample this population to verify completeness.
- Attendance Sheets for Live Sessions: For any in-person or virtual live training, you must have evidence of who attended. This can be a physical sign-in sheet or a participant list exported from the video conferencing tool.
Proper documentation is a key differentiator. It is estimated that 18% of employees globally have never received any cybersecurity training. Demonstrating a well-documented program immediately signals a higher level of security maturity to your auditor.
Demonstrating Continuous Improvement with Data
For a SOC 2 Type 2 report, which covers a period of time, demonstrating continuous improvement is powerful evidence. Data from ongoing security activities, such as phishing simulations, tells a compelling story of progress.
The most powerful story you can tell an auditor is one of measurable improvement. Showing a data-driven reduction in employee risk over the audit period is the ultimate proof that your training program is not just active, but effective.
Track and report on these two key metrics from your phishing simulations:
- Click Rate: The percentage of employees who clicked a malicious link in a simulated phishing email. Your goal is to show a steady downward trend quarter-over-quarter.
- Report Rate: The percentage of employees who correctly reported the phishing email using your defined incident reporting process. A rising report rate is a strong indicator of a positive security culture.
Present this data in a simple chart. Showing that your click rate dropped from 25% in Q1 to 8% in Q4 provides concrete, quantitative proof that your SOC 2 employee security awareness training is effectively reducing risk. This is the kind of evidence auditors value highly.
Organizing Evidence for a Smooth Audit
Disorganized evidence signals to an auditor that your internal controls may also be chaotic. A simple, logical folder structure is sufficient. Create a top-level folder such as “SOC 2 Security Awareness Training Evidence” with subfolders for each audit period.
Within each period’s folder, organize by artifact type:
/Training_Materials/Policy_Acknowledgements/Completion_Reports_(by_Year-Quarter)/Phishing_Simulation_Results
This structure allows you to respond to auditor requests in minutes, not hours. For a deeper dive into managing all your audit evidence, our guide on organizing all your SOC 2 documentation provides a comprehensive framework.
Ultimately, connecting your training program to audit readiness comes down to documentation. Your evidence must prove that a security-conscious culture is not just an aspiration but a documented, measurable, and operational reality at your company.
Common Training Pitfalls That Jeopardize SOC 2 Compliance
A common pitfall that leads to an audit finding is the use of generic, “check-the-box” training that is not tailored to the organization’s specific risks as identified in its risk assessment. Auditors are trained to spot off-the-shelf content that has not been customized. This approach fails to meet the intent of the SOC 2 requirements, which is to mitigate your specific risks through targeted education.
Another critical error is operating a training program that is disconnected from your own documented policies. Why does this matter for someone pursuing SOC 2? Because if your training on incident response doesn’t match your actual Incident Response Plan, or your data handling module contradicts your Data Classification Policy, it demonstrates a severe lack of internal consistency. This is a major red flag for auditors, as it indicates that security controls are not coherently designed or implemented.
The New Hire Vulnerability Window
A frequent and dangerous failure is delaying security training for new hires. Many organizations wait for the next annual training cycle, leaving a vulnerability window open for weeks or even months. This means your newest team members are operating without knowledge of critical security policies.
To a SOC 2 auditor, this is a clear control failure. The expectation is that security training is an integral part of the onboarding process and is completed within the first 30 days.
An auditor will often sample your list of new hires from the HR system and cross-reference it with training completion dates from your LMS. A significant lag between a hire date and a training date is an easily identifiable control deficiency that directly contradicts the principle of maintaining a consistent control environment.
The corrective action is to integrate security awareness training directly into your HR onboarding workflow. Use an LMS to automatically assign the required courses on an employee’s first day, and configure automated reminders and escalations to the employee’s manager if the training is not completed within the mandated 30-day timeframe.
Inconsistent and Unverifiable Record-Keeping
This is the most common and easily avoidable pitfall: poor record-keeping. An excellent training program is worthless from an audit perspective if you cannot produce verifiable evidence of its execution. Inconsistent, incomplete, or missing records make it impossible to prove to an auditor that your control is operating effectively.
This issue manifests in several ways:
- Manual Tracking Failures: Using spreadsheets to track training completion is highly prone to error. Data entry mistakes, lost files, and version control issues make it nearly impossible to prove 100% completion with confidence.
- No Version Control on Materials: Failing to retain dated copies of the training materials (slides, videos) used during the audit period. An auditor needs to inspect the content that was delivered to ensure it was relevant and comprehensive.
- Missing Proof of Attendance: Forgetting to collect sign-in sheets for in-person training or export participant lists from virtual sessions. Without this, there is no verifiable proof of who attended.
The solution is to centralize and automate evidence collection. An LMS is the best tool for this, as it generates immutable, time-stamped reports on demand. For any remaining manual processes, establish a rigid procedure for collecting, reviewing, and storing evidence in a single, organized repository that is immediately accessible during an audit.
This structured approach to documentation is fundamental for being audit-ready. It demonstrates that your SOC 2 employee security awareness training is not just an activity but a managed, monitored, and verifiable control that directly satisfies an auditor’s need to validate the consistent enforcement of your control environment.
A Final Checklist for Audit-Ready Security Training
A mature, well-documented security awareness program is a non-negotiable prerequisite for a clean SOC 2 report. It serves as your most direct evidence that you have successfully established a security-conscious culture, directly satisfying a key principle auditors evaluate under CC1.2 (Control Environment). This checklist is your final self-assessment to ensure your program is not just operational, but auditable.
Before facing an auditor, walk through these checkpoints. They cover the pillars an auditor will examine: your policies, the training content, delivery and tracking mechanisms, and the organization of your evidence.
Policy and Documentation Foundation
Your training program must be built upon a foundation of formal, documented policies. This is the first thing an auditor will request to understand the established rules of your security environment.
- Information Security Policy: Is your primary Information Security Policy formally approved, published, and accessible to all employees? Does it explicitly mandate security awareness training for all personnel?
- Signed Acknowledgements: Can you produce a record for every employee demonstrating they have read and acknowledged the information security policy upon hire?
- Training Program Documentation: Do you have a formal document outlining the security awareness training program itself? This document should define the program’s scope, objectives, curriculum topics, and required frequency, proving it is a planned and structured control.
Content and Curriculum Relevance
Generic training is a red flag. Your program must be tailored to your organization’s specific risks and employee roles. An auditor needs to see a clear connection between the training provided and the systems and data you are protecting.
A common audit request is to “walk through” the training materials. Be ready to show the actual slide decks, videos, and quizzes you use. The auditor is checking to see if the content matches the policies you claim to enforce.
Here are the key checkpoints for your content:
- Core Topics Covered: Does your general training curriculum cover the non-negotiable topics: phishing, password security, secure data handling, and incident reporting procedures?
- Role-Specific Modules: Have you implemented specialized training for high-risk roles, such as secure coding for engineers and BEC fraud prevention for finance?
- Alignment with Risks: Can you articulate how your training topics directly map to the key threats identified in your organization’s formal risk assessment?
Delivery and Tracking Consistency
The methods used to deliver and track training are critical for proving the operating effectiveness of this control, especially for a SOC 2 Type 2 report. Inconsistent delivery or messy tracking makes it impossible to demonstrate continuous operation.
- New Hire Training: Is every new employee automatically enrolled and required to complete training within a defined period, such as their first 30 days? Can you provide LMS reports to prove this?
- Annual Refresher Training: Do you have a documented process to ensure 100% of employees complete refresher training annually? Can you produce the completion reports to verify this?
- Evidence of Completion: Are your training records detailed and auditable? They must include employee names, completion dates, and ideally, quiz scores to demonstrate comprehension.
A meticulously planned and documented SOC 2 employee security awareness training program provides powerful, direct evidence to your auditor that security is a managed and operational discipline within your organization. Successfully implementing and proving this control not only smooths your path to a clean audit report but also fundamentally strengthens your defense against real-world threats. It demonstrates your commitment to protecting customer data and upholding the trust at the core of the SOC 2 framework, confirming your readiness for the audit process.
Finding the right auditor is as critical as preparing for the audit itself. At SOC2Auditors, we replace the stressful, time-consuming search with a data-driven matching process. Get transparent pricing, timelines, and verified reviews to choose your ideal audit partner with confidence. Find your auditor match here.